Security stocks are tanking. CISOs are calling emergency meetings. LinkedIn is on fire with hot takes. Here at AppSecAI, we're genuinely confused about what everyone is so surprised about.
In case you missed it: Anthropic just announced a model called Mythos that found over 1,000 vulnerabilities in well-known open source projects, including 20-year-old security flaws that human pen testers missed for two decades. It can chain five separate vulnerabilities together to find attack paths that no individual would ever connect. The security industry, to put it gently, lost its mind.
Zscaler dropped from $139 to $116 in two days. Not because anything they do changed. Just vibes.
The Pen Testing Math Nobody Wanted to Do
Here's the thing about a $10,000-to-$15,000+ annual penetration test: you were mostly paying for the certificate at the end. The SOC 2 checkbox. The "we tried to break it and couldn't" document that lives in a compliance folder nobody opens.
The actual vulnerability-finding capability? The AI has been getting there for a while. Anyone paying attention knew this was coming. The timing was uncertain. The direction was not.
What Mythos exposed (more than any of those open source flaws,) is how fragile a business model looks when its entire value is "a smart human tried to break your thing." When a prompt can now do the same job in tokens instead of billable hours, the math changes fast...and the math was already broken before this week.
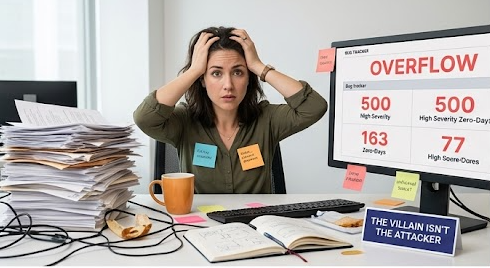
According to Veracode's 2026 State of Software Security Report, the median time to fix a known vulnerability is 243 days. Not finding it. Fixing it. In the meantime, SAST and DAST scanners are dutifully flagging every issue, adding them to backlogs that grow faster than any team can clear them. At a 5% annual fix rate, you mathematically never get below 8,000 open vulnerabilities. Not in your career. Not ever.
Finding was never the problem. It was never going to be the problem.
What Mythos Actually Confirmed
Mythos is impressive. The marketing around it, though, is worth reading carefully.
Anthropic announced 1,000+ vulnerabilities found in open source projects. They did not publish their false positive rate. They did not disclose token costs per finding. They did not explain how many human-hours went into triage and validation. They used human engineers to manually create pull requests for the 500+ they disclosed last month, not their own automated fix technology.
That's not a criticism. It's just a reminder that "we found a lot of things" and "we fixed them reliably at enterprise scale" are two very different sentences.
We built AppSecAI around the second sentence.
The Part Nobody's Talking About
Here's what actually matters after the Mythos announcement: your backlog didn't get smaller. In fact, it's about to get larger. AI-powered vulnerability discovery (from Anthropic, from Google, from OpenAI, from the next tool that drops this week on GitHub,) means finding is going to get faster, cheaper, and more comprehensive. Great.
Now what?
Your developers still don't want to fix security bugs. They're busy learning the AI tools that keep their jobs. Your AppSec team is still triaging false positives. Your SAST and DAST scanners are still generating more findings than any team can action. And the 11-step manual remediation process; scan, triage, assign, track, code, test, rework, integrate, deploy, and close, still requires a human at every step.
The vulnerability-finding era is ending. The vulnerability-fixing era has been waiting for everyone to catch up.
The Actual Takeaway
We're not nervous about Mythos. We think it's excellent news. Every AI lab becoming a vulnerability-finding machine validates what we've believed since we founded this company: the market is moving from "find" to "fix," and it's moving fast.
The enterprises with 10,000 open vulnerabilities aren't worried about finding more. They need something to actually close them: at speed, at scale, with accuracy they can verify.
That's the problem we've been working on. The rest of this is just noise.
If you want to calculate what your current cost-per-fix actually is, it's almost certainly between $5,000 and $20,000, there's a calculator on our website. The number is usually worse than people expect. The gap between that number and what AI-powered remediation costs is where the real story is.
AppSecAI automates vulnerability remediation (triage and fix) with 97% triage accuracy and an average human review time of 8.2 minutes per fix. Pay per fix, not per scan. Learn more here.